-
 How to compute MD5 Hash (Message-Digest algorithm 5) using Cryptography? - .Net | MVC | HTML Agility Pack SQL | Technology Crowds
How to compute MD5 Hash (Message-Digest algorithm 5) using Cryptography? - .Net | MVC | HTML Agility Pack SQL | Technology Crowds
ID: oNl4o3EBoq
From: technologycrowds.com
-
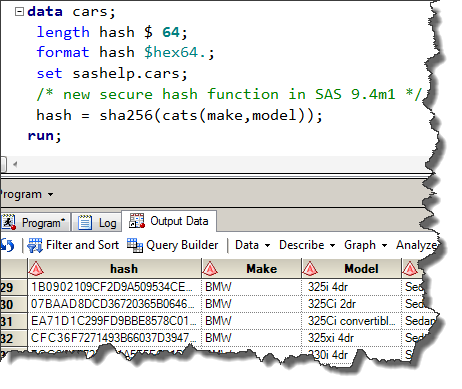 A fresh of hash: the SHA256 function in 9.4 - The SAS Dummy
A fresh of hash: the SHA256 function in 9.4 - The SAS Dummy
ID: eMhTa5YkLo
From: blogs.sas.com
-
![Is Cryptographic Hash? [a Beginner's Guide] Is Cryptographic Hash? [a Beginner's Guide]](https://techjury.net/wp-content/uploads/2020/06/Hashing-a-folder-1.png) Is Cryptographic Hash? [a Beginner's Guide]
Is Cryptographic Hash? [a Beginner's Guide]
ID: sYz305h73y
From: techjury.net
-
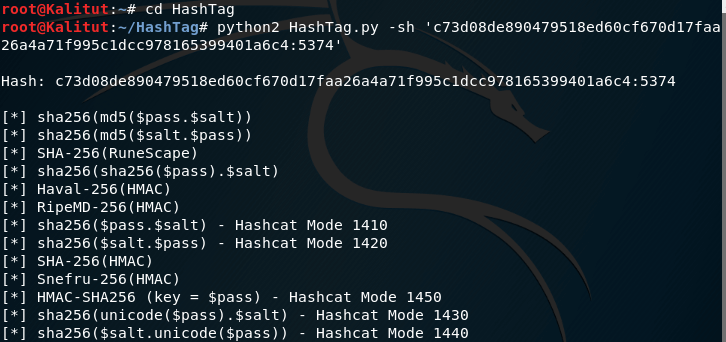
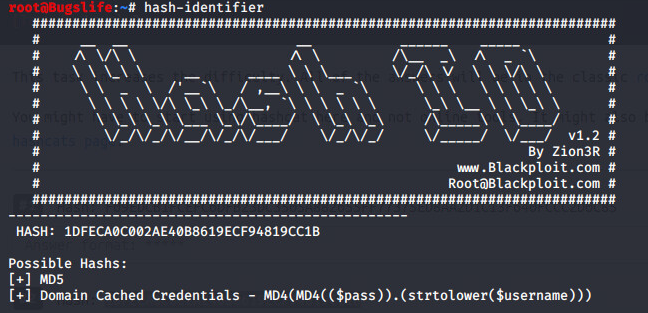
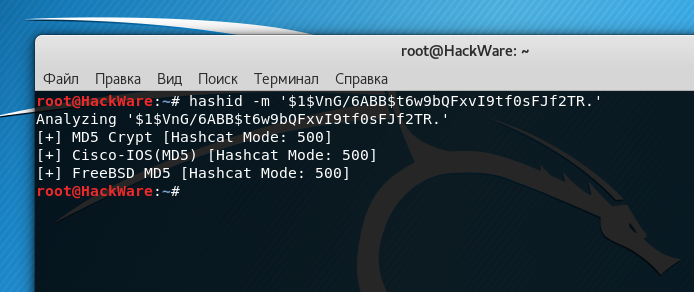 How to identify hash types - Ethical and testing
How to identify hash types - Ethical and testing
ID: YL7Oly8hfN
From: miloserdov.org
-
 How to identify hash types - Ethical and testing
How to identify hash types - Ethical and testing
ID: WnqwErGr8s
From: miloserdov.org
-
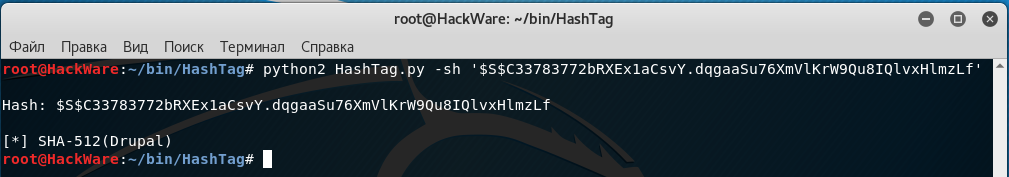
 How to identify hash types – new tools with modern hashes support - and penetration testing
How to identify hash types – new tools with modern hashes support - and penetration testing
ID: qXNNlVvPes
From: miloserdov.org
-
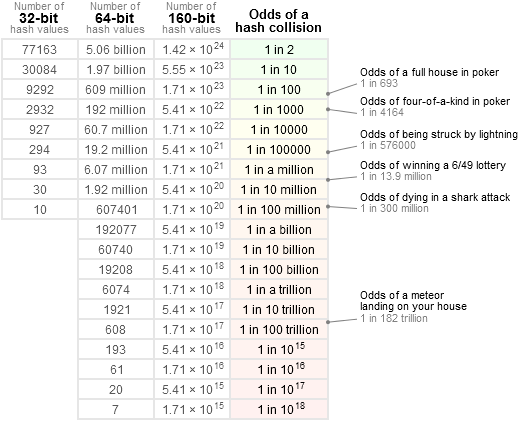 Hash Collision
Hash Collision
ID: rFpBHr3LQ0
From: preshing.com
-
Identifying and Cracking During a penetration or a simple… | by Mr. Robot | InfoSec Adventures |
ID: rQ8fGCWx7S
From: medium.com
-
 Algorithms | Jscrambler
Algorithms | Jscrambler
ID: ewFcUU9j4p
From: blog.jscrambler.com
-
 Illustrated Guide to Cryptographic Hashes
Illustrated Guide to Cryptographic Hashes
ID: gQCX6gNbFO
From: unixwiz.net
-
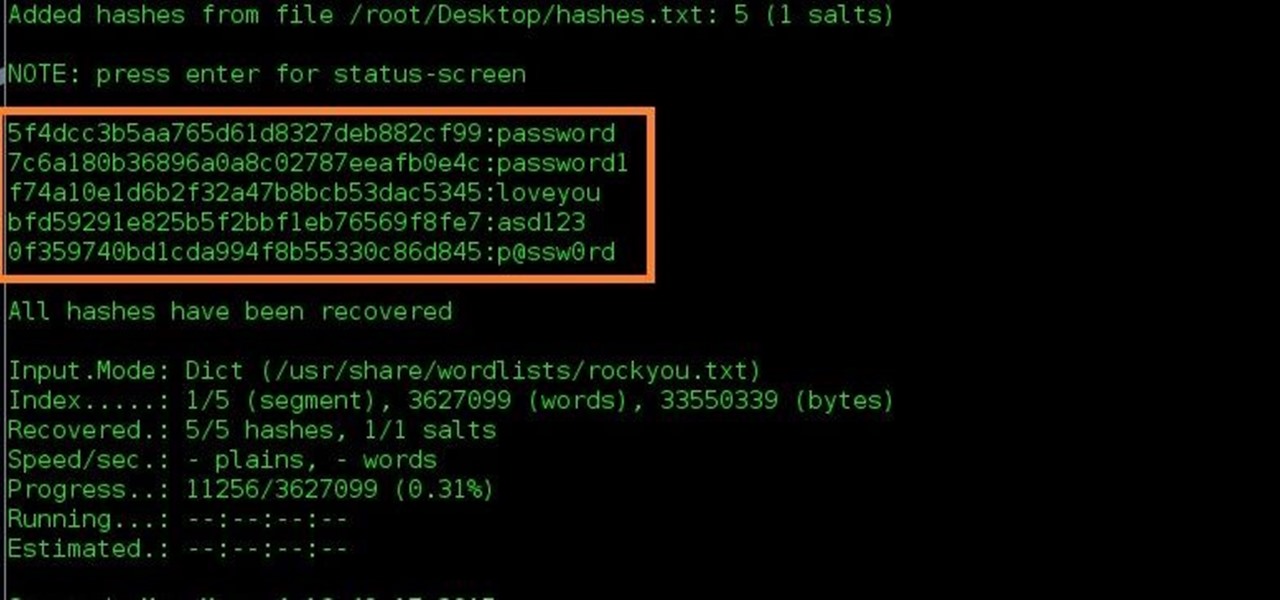 How to Crack Hashes Byte :: WonderHowTo
How to Crack Hashes Byte :: WonderHowTo
ID: wbzRTMszdN
From: null-byte.wonderhowto.com
-
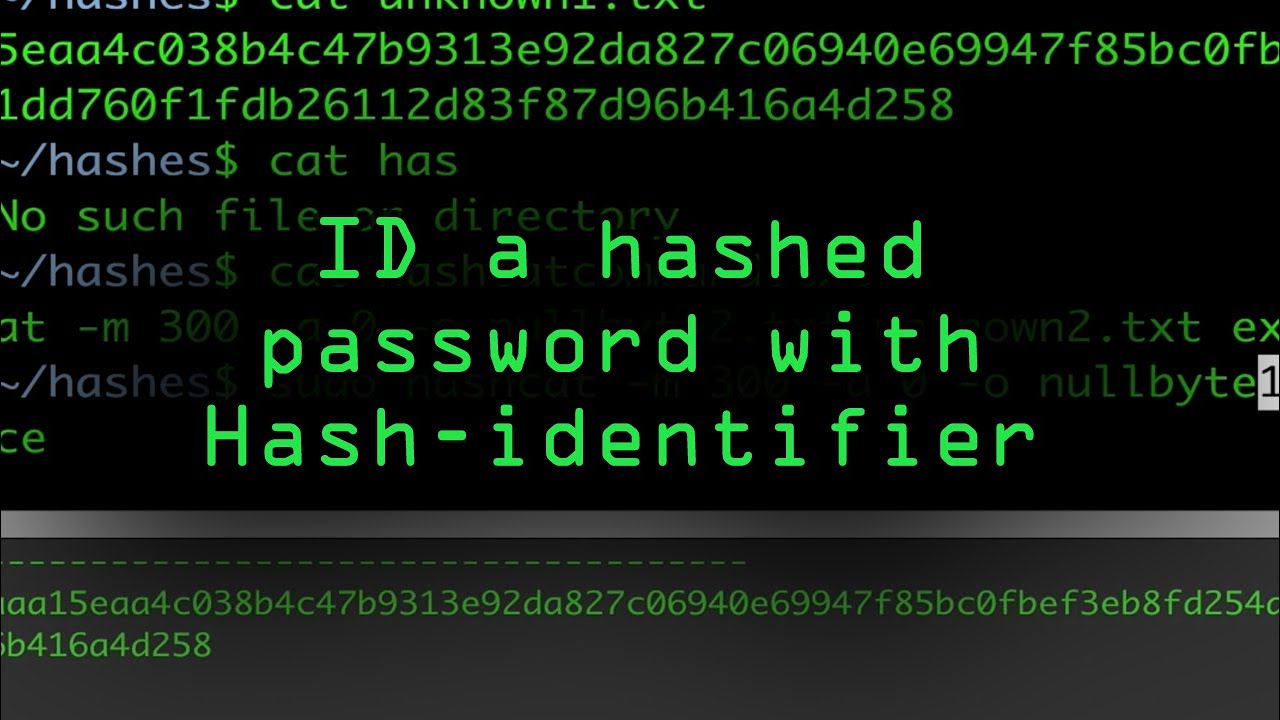 Use Hash-Identifier to Determine Hash Types for Cracking « Byte :: WonderHowTo
Use Hash-Identifier to Determine Hash Types for Cracking « Byte :: WonderHowTo
ID: ty4KojuUFr
From: null-byte.wonderhowto.com
-
 - Crack The Hash CTF »
- Crack The Hash CTF »
ID: e88WhZez2r
From: cyber-99.co.uk
-
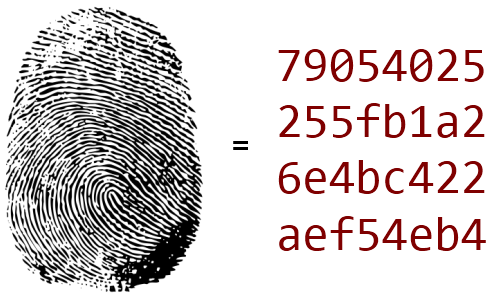
 are hashes and how are they -
are hashes and how are they -
ID: ty7RL8cOCw
From: kalitut.com
-
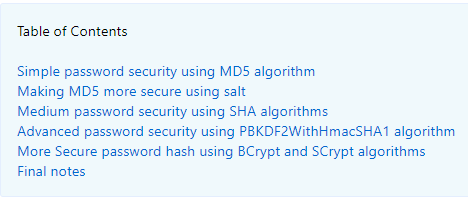 - Create a Secure Password - HowToDoInJava
- Create a Secure Password - HowToDoInJava
ID: xGF9h2I2aB
From: howtodoinjava.com
-
 Speed
Speed
ID: PSzxXsWWPB
From: blog.codinghorror.com
-
 How to Crack Hashes Byte :: WonderHowTo
How to Crack Hashes Byte :: WonderHowTo
ID: eUP7Sz6yO1
From: null-byte.wonderhowto.com
-
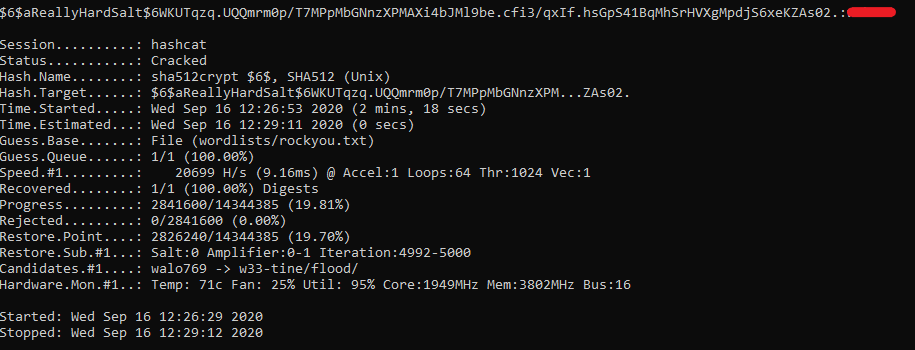
![Hashcat beginners [updated 2021] - Resources Hashcat beginners [updated 2021] - Resources](https://resources.infosecinstitute.com/wp-content/uploads/2018/04/122120-2.png) Hashcat beginners [updated 2021] - Resources
Hashcat beginners [updated 2021] - Resources
ID: ujLN6XWUdB
From: resources.infosecinstitute.com
-
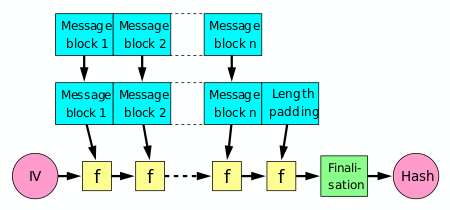 Cryptographic hash function Wikipedia
Cryptographic hash function Wikipedia
ID: 7NO1b1u7vs
From: en.wikipedia.org
-
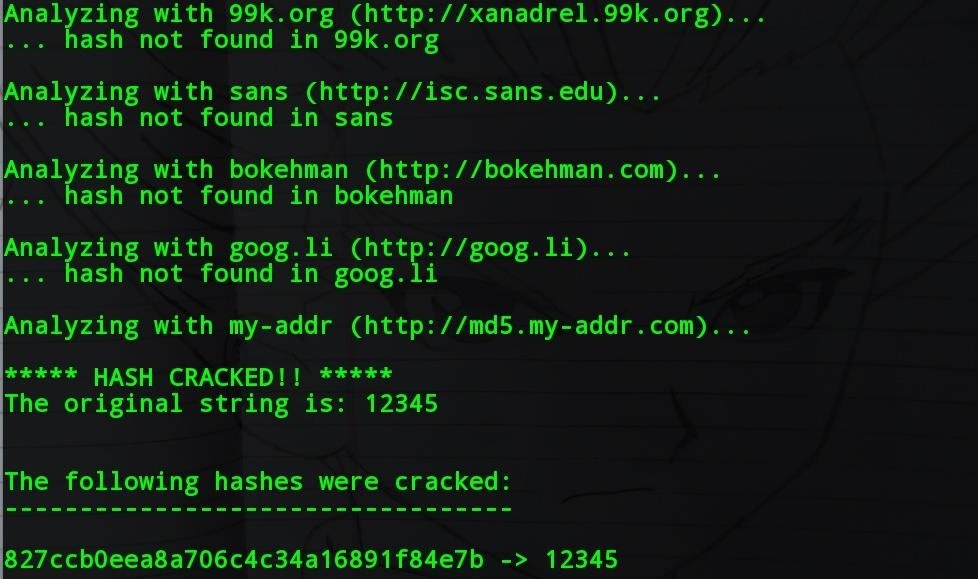 How to Crack Hashes Byte :: WonderHowTo
How to Crack Hashes Byte :: WonderHowTo
ID: lLE13j91KN
From: null-byte.wonderhowto.com
-
 Identifying and Cracking During a penetration or a simple… | by Mr. Robot | InfoSec Adventures |
Identifying and Cracking During a penetration or a simple… | by Mr. Robot | InfoSec Adventures |
ID: YT7qf2viWF
From: medium.com
-
 - Crack The Hash CTF »
- Crack The Hash CTF »
ID: R7avqTg5Rz
From: cyber-99.co.uk
-
 What is Why cryptographers | by Liberty York | Tech Tales | Medium
What is Why cryptographers | by Liberty York | Tech Tales | Medium
ID: JFDyh27gKw
From: medium.com
-
 KALI – How to crack passwords using Hashcat – The Visual Guide | University of South Wales: Cyber University of the year: years running: 2019, 2020, 2021
KALI – How to crack passwords using Hashcat – The Visual Guide | University of South Wales: Cyber University of the year: years running: 2019, 2020, 2021
ID: oC4RO8kFMF
From: uwnthesis.wordpress.com
-
 Algorithms | Jscrambler
Algorithms | Jscrambler
ID: MnVSKIkTti
From: blog.jscrambler.com
-
 One-Way Hash Function - an overview | ScienceDirect
One-Way Hash Function - an overview | ScienceDirect
ID: S83YYNTcU3
From: sciencedirect.com